Securing internet system becomes very challenging with the passage of time as more technological systems are getting connected to the internet. It is commonly observed that malwares are gradually entering the internet market with each addition of IT systems. The malware is hazardous in a sense that it indirectly affects computer networks by sending phishing emails and disclosing very confidential information. In other words internet is no more secure for those having personal data shared for their own purposes. It is very necessary to understand the behaviour of malware and how it affects the users. Therefore we need to have an automated analysis which might help us in overcoming the malware attacks. Sandbox analysis which is considered one of the most promising automated analysis is a tool to detect malwares and it can also help in halting malicious files which might be harmful for an individual with his priorities on the internet.
MALWARE SANDBOX
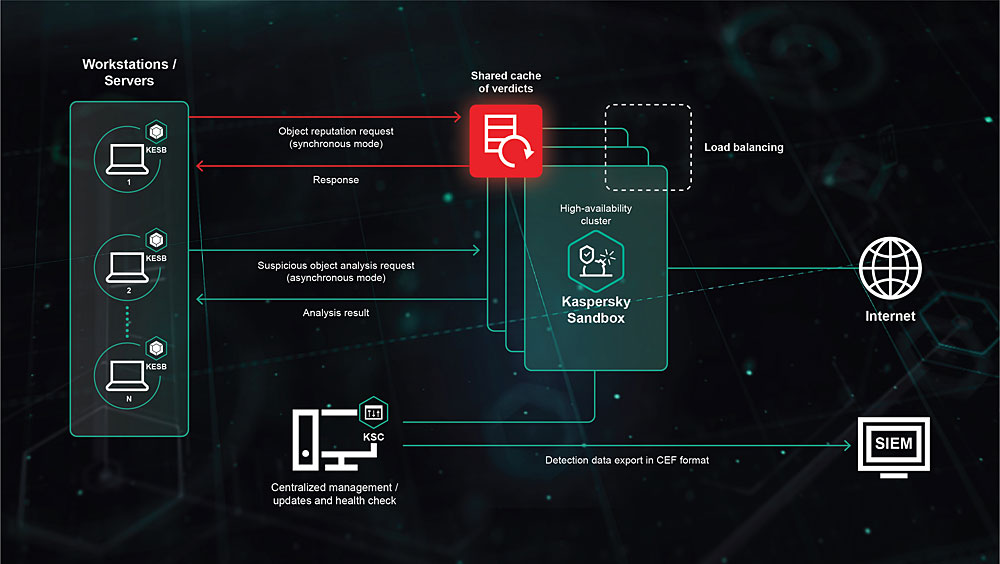
Malware sandboxes are one kind of automated analysis which uses a malware sample enacted in a testing atmosphere. The malware sandbox is specifically designed to precisely observe the behaviour of malware. There are various features of malware sandbox which makes it dissimilar to the human analysis. When it comes to human analysis in detecting malwares it requires a highly skilled reverse engineering techniques which is very time consuming and difficult to carry out. Malwares using sandbox analysis can be detected in two different ways. First the victim host is connected to the real internet and in the second way the victim is completely isolated from the real internet. The former is more desirable in terms of observing diverse activities of malware. The disadvantage of this approach is that attacks from the infected host may exit the sandbox.
Criteria for malware sandbox
Malware sandboxes relies on the following criteria
- OBSERVABILITY
As it is essential to write a signature for anti-virus software as well as removal tools therefore we need to analyse malware feasibility such as observing the internal behaviour of malware which involves file creation and registry alteration. On contrary to that, it is very important to observe the network behaviour of malwares as they can be used to disclose and block malevolent traffic to exacerbate the propagation.
The observability relies on the following six components.
- First victim
The examined malware sample is first executed.
- Second victim
The malware executed in the first victim is brought to the second victim to be infected.
- Internet emulator
As we know that the sandbox is totally isolated from the real internet, the internet emulator is there to deceive the malware into thinking they are not in our testing atmosphere.
- Distinguisher
This functionality distinguishes whether the traffic from the first victim needs to be sent to the second victim or internet emulator. It updates all incoming information from the first victim and decide where to pass them.
CONCLUSION
The malware sandbox utilises two victim hosts to observe vulnerability exploitation by malware. Furthermore it is capable of observing propagation of all the pre-programmed malware samples. Certain limitations are there which we can overcome in the near future.
Limitations includes distinguishability, internet emulation, detection of exploit codes and diversity of vulnerabilities.